Where open innovation meets secure operations
Every open-source ecosystem runs on trust. But trust only holds when security is engineered into governance, funding, and contributor systems from the ground up — not bolted on after the first incident.
The Outrider Practice exists for ecosystems, foundations, and organizations that have crossed from experimentation into infrastructure. At that inflection point, informal security arrangements break down. Coordination gaps surface. Responsibility diffuses. Incidents stop being isolated events and become systemic risks.
Outrider addresses this reality directly, integrating security into how open ecosystems are governed, funded, and operated — aligning technical controls with real decision rights and accountability structures.
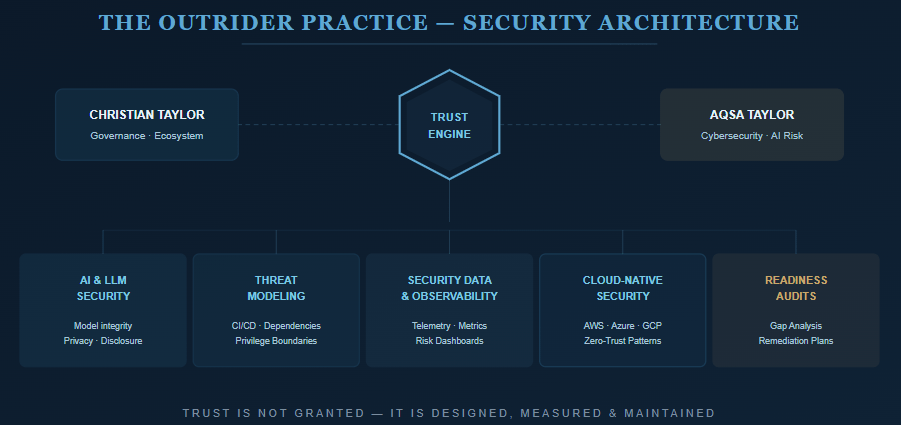
Two Complementary Disciplines
Christian Taylor — Governance & Ecosystem Architecture
Designs and operates governance, funding, and program systems that allow open source ecosystems to scale across contributors, vendors, and institutions. His work focuses on authority, accountability, and survivability under real-world pressure.
Aqsa Taylor — Strategic Advisor, Cybersecurity
A cybersecurity and AI risk strategist with experience securing complex, distributed environments across enterprise and open ecosystems. Currently Chief Research Officer at SACR, leading research on AI security, data trust, and hybrid infrastructure.
Previously held senior roles at Abstract Security, Gutsy, and Palo Alto Networks (Prisma Cloud / Twistlock). Author of Applied Security Data Strategy and Process Mining: The Security Angle.
As Strategic Advisor for the Outrider Practice, Aqsa ensures every engagement meets rigorous standards for cybersecurity, privacy, and operational assurance.
Security Consulting Services
1. AI & LLM Security Strategy
Governance and security models for AI systems operating in open or hybrid environments — including risk analysis across data pipelines, model integrity controls, privacy-preserving architectures, and responsible disclosure frameworks.
Outcome: Secure, accountable AI adoption aligned with open-source principles and enterprise-grade assurance.
2. Ecosystem Threat Modeling & Architecture Reviews
Design-level security analysis across multi-repository ecosystems and governance infrastructure, covering contributor workflows, privilege boundaries, CI/CD integrity, dependency chains, and governance tooling.
Outcome: A threat model and architecture blueprint aligned to operational reality.
3. Security Data Strategy & Observability
Security telemetry and data pipelines connecting governance performance to security posture, with readiness scoring, ecosystem-wide metrics, and governance dashboard integration.
Outcome: Measurable, real-time visibility into ecosystem risk and resilience.
4. Cloud-Native & Infrastructure Security
Hardening AWS, Azure, and GCP environments supporting open development — including IaC audits, identity and secrets management, secure build pipelines, and zero-trust patterns for distributed contributors.
Outcome: Repeatable security frameworks that preserve openness without sacrificing control.
5. Security Readiness Audits & Advisory
Independent security posture assessments for open ecosystems, DAOs, and technical foundations, with policy review, operational gap analysis, governance-aligned remediation, and workshops. Fractional advisory support available for long-term alignment.
Outcome: A defensible security posture that scales with governance maturity.
Why It Matters: As ecosystems grow, trust cannot rest on goodwill or informal norms. It must be engineered into governance, funding, and operations. The Outrider Practice builds those systems — not to slow ecosystems down, but to ensure they endure.
“In open ecosystems, trust is not granted. It is designed, measured, and maintained.”
It is designed, measured, and maintained.